Privileged access management is an important concept to understand as a business owner. The proliferation of privileged accounts across all devices makes it difficult for organizations to keep track of who’s who and what they’re doing on their network. This article provides some of the benefits and challenges associated with privileged access management, including some of the ways that you can invest in this type of solution. Overall, privileged access management services improve the security and efficiency of your organization’s operations by protecting valuable data and assets while facilitating effective communication and collaboration between employees
Introduction
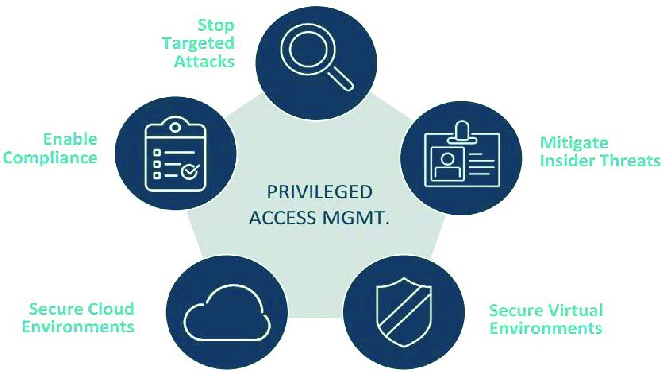
Privileged access management services are essential for organizations that need to control who has access to sensitive data and information. PAM services can help protect data from unauthorized access, prevent insider threats, and ensure compliance with stringent privacy and security regulations.
Organizations that need to manage privileged access typically employ a centralized authentication and authorization system. This system collects user credentials, determines which users have the necessary permissions, and authenticates users before allowing them to access resources. However, this approach can be difficult to administer and maintain, particularly when changes need to be made to the system.
Instead of relying on a centralized authentication and authorization system, many organizations now use an open-source PAM solution called SAML 2.0. This solution relies on standard XML documents to authenticate users and authorize them for access to resources. Because SAML 2.0 is an open standard, it can be integrated into a variety of applications and systems.
If you’re looking for a solution that can help protect your data from unauthorized access, privileged access management services are an essential investment.
What is Privileged Access Management?
Privileged access management (PAM) is a way to manage and control access to information and resources. It is used in organizations to protect the privacy of individuals and the confidentiality of information. PAM can also help reduce the risk of data theft, identity theft, and other cyberattacks.
Typically, privileged access means to access that is different from the general public or employees who are not authorized to have it. This access can be granted by an individual or organization for a specific purpose, such as performing a job function or accessing confidential information.
One of the benefits of using PAM is that it can help reduce the risk of unauthorized users accessing sensitive data or equipment. It can also help prevent employees from inadvertently sharing confidential information with unauthorized third parties.
In order to create a secure environment, PAM tools must be properly configured and managed. Properly configured PAM tools will allow administrators to effectively restrict user access while still allowing them to perform their job duties. Furthermore, proper management of PAM tools can help ensure that they are up-to-date and compliant with all current regulations.
Benefits of Privileged Access Management
When it comes to safeguarding your business’s confidential information, privileged access management (PAM) is a must-have service. Here are four reasons why you need PAM in your digital arsenal:
1. Prevent data breaches. With sensitive data scattered all over the web, cybercriminals are always looking for an opportunity to steal your secrets. By implementing PAM, you can help prevent unauthorized access to your data by granting only specific individuals access to certain areas of your website or system.
2. Enhance security posture. By controlling who has access to which resources, you can help protect your systems against malicious actors and malware. For example, if someone within your company video from the corporate server without authorization, PAM could help trace the illicit activity back to them – potentially saving your company a lot of embarrassment and damage.
3. Minimize legal liability. One of the most important benefits of PAM is that it can help you avoid legal liability for losses caused by unauthorized access to confidential information. By establishing clear policies and procedures for managing privileged access, you can avoid potential lawsuits from disgruntled employees or contractors who misuse their privileges inadvertently.
Privileged access management services protect your organization’s information and assets by controlling who has access to what. PAM services can help you:
1. Keep sensitive data safe: PAM helps to ensure that only authorized personnel has access to company information and resources. When a user is unable to provide the proper level of authorization, they may be prevented from accessing critical data or systems.
2. Prevent unauthorized use of resources: By restricting certain users from accessing certain resources, you can prevent malicious actors from exploiting vulnerable systems or stealing confidential information.
3. Maintain compliance with regulations: By properly managing access privileges, you can reduce the risk of regulatory violations. In some cases, even inadvertent disclosure of confidential data can result in fines or other penalties.
4. Improve employee productivity: Privileged access management can help employees work more effectively by ensuring that they have the correct permissions to perform their job duties. This reduces the amount of time needed to obtain the necessary permissions and enables employees to focus on their work instead of navigating complex security procedures.
Features of Privileged Access Management Services
One of the key factors to consider when choosing a privileged access management service is the features offered. Some of the features that are typically included are:
1. Role-based access management: This allows administrators to assign different levels of access to users, based on their role in the organization. This can help to ensure that only authorized users have access to sensitive information.
2. Audit trails: A privileged access management service will keep track of all activity and access logs so that administrators can track who has accessed what and when. This helps ensure accountability and transparency for all activities within the organization.
3. Security controls: A privileged access management service will provide security measures such as firewalls, intrusion detection systems (IDS), and password protection, to keep data safe from unauthorized access.
Who Provides Privileged Access Management Services?
Privileged access management (PAM) services are necessary for organizations that deal with confidential or proprietary information. PAM services can help protect your organization from unauthorized access to its data, systems, and networks.
The most common types of PAM services are authentication, authorization, and accounting (AAA). Authentication helps identify users who are authorized to access systems. Authorization determines whether a user is allowed to perform certain actions on systems. Accounting records the activities of authorized users on systems.
There are several different PAM providers available. Some providers specialize in providing only one type of PAM service. Others offer a comprehensive suite of PAM services. Choosing the right provider is important because not all providers have the same capabilities and features.
Some factors to consider when selecting a PAM provider include the following:
-The provider’s experience with protecting sensitive data
-The provider’s ability to integrate with other security solutions
-The provider’s customer service and technical support
-The price of the PAM service
Also Read: Best Business Opportunities
Conclusion
Privileged access management services are a critical part of any business’ security strategy. Not only can they help to keep your data safe and secure, but they can also help you to comply with regulations like the GDPR. If you’re not already using privileged access management services, I urge you to start today. They won’t cost much and they could mean the difference between a disaster and a successful business operation.