Today we’ll be discussing the unique technique of unlimited SMS sending, also known as SMS Bombing. How do you use it? This tool can be used in kali Linux, Windows, and MacOS. Let’s get started!
SMS Bombing & Call bomber
Many APIs were killed by TBomb misuse. If you don’t receive all the messages, don’t worry. Call bomber
- To run the script, you must have a working network connection.
- This script is free to use for sending SMS/calls.
- For maximum performance, infinite bombing should be performed with a delay of 2-3 seconds and 10-20 threads.
- Do not put spaces between the phone number (Ex-99999 99999).
- Make sure that you have the most recent version of TBomb
- You must ensure that Python3 is used Call Bomber & SMS Bomber in any number Custom sms bomber
Here’s how to check it. This command should be entered in your terminal.
python -V
Features:
- Many integrated SMS/call APIs
- Unlimited (Limited to Abusing) and super-fast Bombing
- International bombing is possible (APIS Dead). Try Your Luck.
- Bombing is a crime
- Frequent updates
- Automated updating
- It is easy to use and embed code
How to Use? ( LInux )
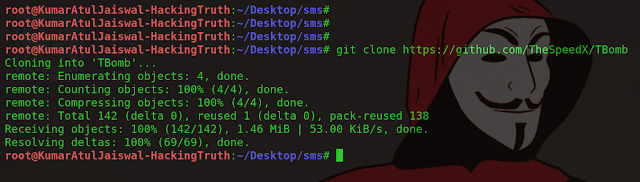
Step 1: First, we must install the sms bombing device so,
git clone https://github.com/TheSpeedX/TBomb
ls
cd
Run
Bash TBomb.sh
Click 1 to Start SMS Bomber
To start a call bomber press 2
Press 3 To Update (Works On Linux And Linux Emulators)
Click 4 to View All Features
To exit, press 5
So, I’ll choose option 1. Press 1 and hit enter.
Enter your Country Code (without +): 91
Enter Target Number: +91 7979 *********
Enter the Number of Messages to Send ( 0 for Unlimited ): 0
Enter delay time (in seconds) [Recommended 2 sec]: 2
Number of Threads (10-20): 19
Then, hit enter
Call bomber
custom sms bomber
sms bomber script
Protection from sms bombers
sms bomber
Android missing tricks
Telegram for sms bomber
sms bomber
turbo bomber
SMS app
Kali linux
For Termux:
Notice:
Git installation methods may not be universal. They can differ from one distribution to another. Check out this guide to installing git on your Linux distribution. These commands are for Debian-based systems.
The following commands can be used to activate the bomber:
- pkg install Git
- pkg install Python
- git clone https://github.com/TheSpeedX/TBomb.git
- cd TBomb
- chmod +x Tomb.sh
- ./TBomb.sh
Alternatively you can use Unlimited call bomber if you are using an android device. This apk also has the same purpose.
MacOS:
Use the following commands to use the bomber:
# Install Brew
/usr/bin/ruby -e “$(curl -fsSL https://raw.githubusercontent.com/Homebrew/install/master/install)”
# Install dependencys:
brew install Git
brew install Python3
sudo easy install pip
sudo pip –upgrade pip
git clone https://github.com/TheSpeedX/TBomb.git
cd TBomb
chmod +x Tomb.sh
# MacOS Missing Tools
Toilets cannot yet be installed. However, TBomb still works.
# Run TBomb:
sudo bash TBomb.sh
Read More: Interested in watching latest movies and shows for free? Download the latest pikashow apk now.
Disclaimer
This article was created for educational purposes and pentest.
Any damage caused by the author is beyond the control of the author.
This tool’s author It is not re Any misuse of the information will be deemed your responsibility.
The information will not be misused to gain unauthorized access.
This information is intended to enhance knowledge, not cause malicious or destructive attacks. Any task can be performed. Hacking without permission is illegal.
Tutorials and videos are intended for educational and informational purposes only. We believe ethical hacking, cyber security, and information security should all be topics that are familiar to everyone. using digital in Computers and formation. It is difficult to protect yourself against hackers if you don’t know how hacking works. These tutorials and videos will help you to understand hacking. This is for people who are interested in learning about security, ethical hacking, and malware analysis. Hacking tutorials are not allowed. The use of th We strongly discourage the use of this information. Every time hacking is mentioned, please consider it ethical hacking or penetration testing.
Tutorials and videos made with our routers, servers and websites, and other resources. They do not contain illegal activity. We don’t encourage, encourage, support, or excite illegal activity or hacking without permission in writing. We aim to increase security awareness and educate our readers about how to avoid becoming a victim to hackers. Please leave this site immediately if you intend to use the information illegally. We are not responsible for any misuse of this information.